Thousands of companies have lost thousands because of one forgotten hard drive.
Often, the IT director thought it was wiped. But it wasn’t, resulting in a costly and publicly embarrassing data leak.
Stories like this are common, and they highlight a growing truth: IT asset disposition is no longer optional.
In today’s high-risk digital world, businesses need airtight systems to manage, sanitize, and retire their equipment. That’s exactly what this guide will help you master.
Explore what ITAD is, why it matters, and how to build a program that protects your business from every angle.
Let’s dive in.
Key Takeaways:
- Retired devices are one of the biggest hidden security risks, and even “wiped” hardware can still contain recoverable data without proper ITAD processes.
- ITAD is a critical part of modern cybersecurity, ensuring secure data destruction, chain-of-custody tracking, compliance, and environmentally responsible disposal.
- Improper disposal can lead to major financial, legal, and reputational damage, including breaches, lawsuits, and regulatory fines from HIPAA, GDPR, and other laws.
- A structured ITAD program protects your entire organization, from servers and laptops to mobile devices and data centers, keeping sensitive data secure from first use to final destruction.
What Is Data Security?
Data security is the practice of protecting your digital information from unauthorized access, misuse, or loss. It covers everything from encryption and access controls to secure hardware handling.
But here’s the catch: data security doesn’t end when a device reaches the end of life.
Old hardware still holds sensitive data like client records, financial reports, and login credentials until it’s properly erased or destroyed. That’s why secure ITAD is a foundational part of modern data protection.
Data Sanitization
Data sanitization is the deliberate, permanent removal of data from a device. This ensures data cannot be recovered, not even with advanced forensic tools.
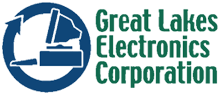
There are a few primary methods:
1. Clearing
Clearing overwrites existing data with meaningless information, so it becomes unreadable.
- Ideal for devices that will be reused or redeployed
- Prevents recovery using standard software tools
- Common for laptops, desktops, and external drives
While effective for certain use cases, clearing isn’t strong enough for highly sensitive or regulated data.
2. Purging
This method uses advanced techniques to permanently erase data, even from devices targeted by forensic recovery tools.
- Cryptographic erasure, destroying encryption keys
- Firmware-level secure erase commands
- Suitable for financial, medical, or personally identifiable information (PII)
Purging leaves the device intact but ensures data cannot be reconstructed.
3. Electromagnetic Pulse (EMP)
EMP uses a concentrated electromagnetic burst to disrupt and destroy data stored on magnetic media, such as hard drives.
- Effective for securely wiping sensitive information from HDDs
- Limited use for SSDs or flash storage
- Typically used in high-security environments where rapid, complete data neutralization is required
EMP is a specialized physical destruction method, supplementing other sanitization processes for added assurance.
4. Physical Destruction
Physical destruction irreversibly damages the storage media, so no data can ever be recovered. Methods include:
- Shredding or pulverizing drives
- Crushing or drilling storage media
- Degaussing magnetic drives
Physical destruction is considered the gold standard for highly sensitive or regulated industries and devices that are no longer operational.
Bottom line? If you want true security, sanitization must be part of every hardware retirement process.
Importance of Data Management & Data Destruction
Proper data management keeps your information organized, secure, and accessible across your organization. But once data is no longer needed, data destruction takes over to eliminate risk.
Here’s why data management and descruction matters.
Every Device Becomes a Liability
Even outdated laptops, servers, or external drives can contain confidential information. Without proper destruction, these devices can expose sensitive data to cybercriminals, putting your business at serious risk of breaches.
Data Privacy Laws Demand Full Lifecycle Management
Regulations like HIPAA, GDPR, and FACTA require organizations to manage and protect data throughout its lifecycle. Compliance doesn’t end when a device is unplugged; you must securely retire, sanitize, or destroy it to meet legal obligations.
Improper Disposal Can Lead to Lawsuits and Reputational Damage
The average cost of a data breach is now about $4.88 million, meaning any breach, including one caused by improper disposal, can have massive financial consequences.
A single data leak from a retired device can trigger costly lawsuits, breach notifications, and long-term damage to your company’s reputation. Your customers, partners, and employees expect their data to be handled responsibly, and your business must deliver.
What Is ITAD?
ITAD (IT asset disposition) is the process of securely retiring, recycling, repurposing, or destroying outdated IT assets. It ensures your organization’s end-of-life technology is managed safely, sustainably, and in full compliance with industry regulations.
A strong ITAD program handles:
- Secure data destruction
- Inventory and chain-of-custody tracking
- Certified recycling
- Hardware value recovery
- Environmental compliance
- Documentation and reporting
Think of ITAD as the final step in your cybersecurity strategy. Because if your old devices aren’t secure, your business isn’t secure.
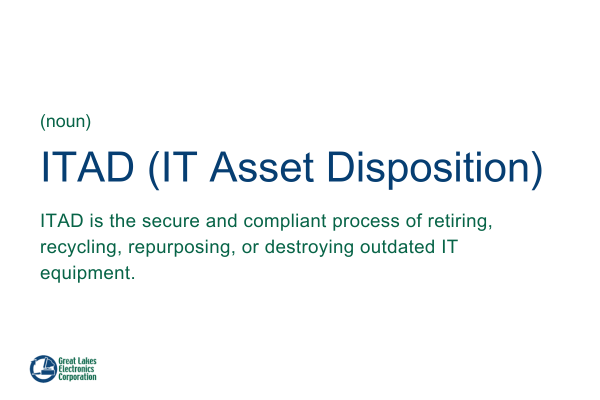
Why ITAD Is Essential for Your Business’s Security
Many businesses assume that once a device is unplugged or retired, the risk disappears. Unfortunately, nothing could be further from the truth.
In fact, risk often skyrockets during hardware retirement. Why? Oversight drops, processes get overlooked, and retired devices become soft targets for cybercriminals. That’s where IT asset disposition comes in as a mission-critical safeguard.
Hard Drives Can Retain Data Even After Basic Wiping
Think formatting a laptop or server deletes everything? Think again.
Even seemingly “clean” drives can retain recoverable data. Advanced forensic tools can extract sensitive files, exposing your organization to cyberattacks, data leaks, and compliance violations.
However, professional ITAD ensures that every device undergoes certified data destruction or sanitization, eliminating any chance of recovery.
Old Equipment Is a Prime Target for Cybercriminals
Cybercriminals know that retired hardware is often neglected. They actively seek out unprotected laptops, servers, and storage devices.
Skipping proper ITAD processes is like leaving your front door wide open. The result? Data breaches, identity theft, and significant financial losses.
ITAD Protects Every Endpoint Across Your Organization
From servers to laptops, phones, and tablets, every endpoint matters. A robust ITAD program ensures that no device is overlooked, whether it’s in a corporate office, a remote employee’s home, or a data center.
This end-to-end approach keeps your entire digital ecosystem secure, from the first byte to the final disposal.
Regulatory Fines Are Increasing Every Year
Data privacy and security regulations are only getting stricter. HIPAA, GDPR, FACTA, and industry-specific standards require full accountability throughout an asset’s lifecycle.
Noncompliance isn’t just risky; it can be financially devastating. Further, fines, audits, and reputational damage can cripple even profitable businesses.
Easy Ways to Improve Your IT Asset Disposition Program
Improving your ITAD program doesn’t have to be overwhelming. With the right strategies, you can strengthen security, stay compliant, and even recover value from old devices.
Here’s how.
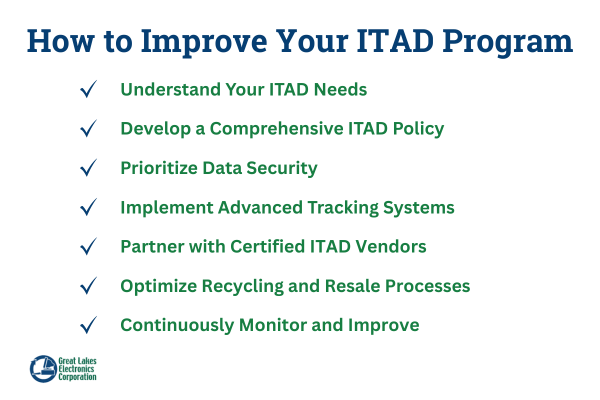
#1: Understand Your ITAD Needs
Before you implement changes, take a full inventory of your IT assets. Ask questions like:
- Which devices store sensitive data?
- How often are assets retired?
- Are remote employees included?
Understanding your ITAD needs sets the foundation for a program that works for your business, not just generic guidelines. A tailored approach reduces risk and prevents costly mistakes.
#2: Develop a Comprehensive ITAD Policy
A written policy is your roadmap for secure IT asset disposition. It should clearly define procedures for device retirement, data destruction, recycling, resale, and chain-of-custody tracking.
Include:
- Roles and responsibilities
- Timelines
- Compliance requirements
Overall, a strong policy ensures consistency and accountability across your organization.
#3: Prioritize Data Security
Data breaches often occur when old devices aren’t fully sanitized. Implement strict data destruction standards like NIST 800-88 and enforce certified destruction for sensitive hardware.
Training employees on data handling protocols ensures no device leaves your organization with recoverable information. Your ITAD program should always put data protection first.
#4: Implement Advanced Tracking Systems
Tracking is key to a successful ITAD program. Monitor equipment from retirement to destruction with
- Barcodes
- RFID tags
- Asset management solutions
Advanced tracking reduces human error, prevents lost devices, and makes audits simpler. Additionally, it shows auditors and regulators that your program is fully transparent and accountable.
#5: Partner with Certified ITAD Vendors
You may have a cheap place you dump your electronics, but not all ITAD vendors are created equal. Choose vendors with certifications such as R2, e-Stewards, and ISO.
Certified partners provide documented proof of destruction, compliance with regulations, and environmentally responsible recycling. This gives your business peace of mind and protects against legal liability.
#6: Optimize Recycling and Resale Processes
ITAD isn’t just about destruction; it’s also an opportunity to recover value. Partner with vendors that responsibly recycle to maximize returns.
Use structured processes to separate devices for resale, donation, or recycling. This reduces environmental impact and turns old assets into new revenue streams.
#7: Continuously Monitor and Improve
ITAD isn’t a set-it-and-forget-it process. Regularly:
- Audit your program
- Evaluate vendor performance
- Gather employee feedback
Technology, regulations, and security threats evolve, so should your ITAD program. Continuous improvement ensures your business stays secure, compliant, and efficient over time.
ITAD Best Practices for Your Business
Implementing a strong ITAD program isn’t just about ticking boxes; it’s about creating a reliable, repeatable system that protects your data and maximizes asset value.
Here are the best practices every business should follow:
Remove Obsolete or Redundant Assets
Start by identifying devices that are outdated, unused, or redundant. Removing these assets reduces clutter, lowers security risks, and frees up physical and digital space.
Regular audits help prevent “forgotten” devices from slipping through the cracks, which is often when data vulnerabilities occur.
Keep Devices Secure
Even retired or soon-to-be-decommissioned devices can be targets for data theft. Physically secure assets in locked storage, restrict access, and monitor handling at every stage.
54% of large enterprises have experienced a data breach due to lost or stolen devices, underscoring how unmanaged or improperly retired hardware remains a major vulnerability.
Security protocols should also cover transportation, especially when devices are moved off-site for destruction or resale.
Get a Certified Compliance Report
Always obtain formal documentation confirming data destruction. Certificates of destruction and compliance reports provide legal proof that your ITAD process was handled responsibly.
These records are essential for audits, regulatory compliance, and demonstrating due diligence to stakeholders.
Risks of Improper Data Destruction
Improper destruction doesn’t just create “possible” problems. It creates guaranteed ones.
Here are the most dangerous risks.
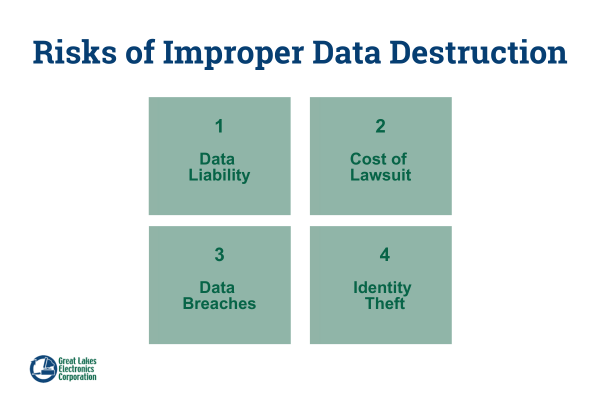
1. Data Liability
Every piece of stored data carries legal responsibility. If that data leaks, the liability falls on your business, not the recycling center, not the courier.
Data liability can result in:
- Regulatory fines
- Breach notifications
- Forced corrective actions
- Long-term brand damage
And it all stems from one thing: poor ITAD.
2. Cost of a Data Breach Lawsuit
A single data breach lawsuit can cost millions. Legal fees, investigations, settlements, and PR recovery all pile up.
The worst part? Most breaches traced back to poor equipment disposal are 100% preventable.
3. Data Breach From Remote Workers
Remote workers store company data on laptops, phones, external drives, and personal networks. When those devices go missing or aren’t properly sanitized, the consequences can be severe.
Remote ITAD is now one of the highest-risk areas for modern organizations. And without a plan, you’re vulnerable.
4. Identity Theft
If personal data reaches the wrong hands, identity theft becomes a real threat. This impacts customers, patients, employees, and partners.
45% of all data breaches involve exposure of sensitive personal information (PII) such as tax IDs, emails, and addresses, illustrating the real stakes of failing to securely retire devices.
Identity theft lawsuits are costly. But the reputational damage? Even worse.
Regulatory Compliance in Data Destruction
Proper IT asset disposition is not just a best practice; it’s a regulatory requirement for organizations that handle sensitive information. Failing to comply with data protection and environmental laws can lead to hefty fines, legal action, and long-term reputational damage.
A certified ITAD program ensures that every retired device is handled securely, documented, and destroyed according to industry and government standards, providing full accountability and audit readiness.
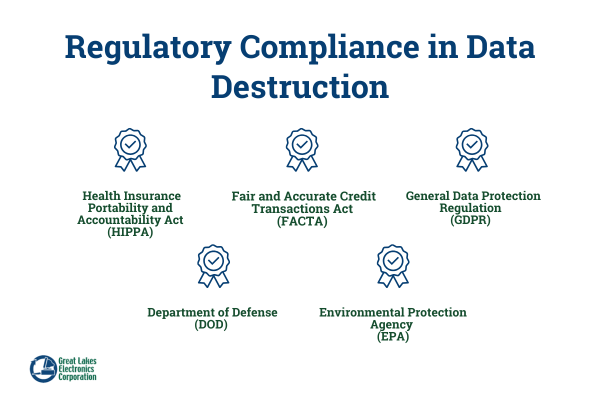
HIPAA
The Health Insurance Portability and Accountability Act (HIPAA) protects patient health information, requiring secure and documented destruction of PHI. Non-compliance can result in massive fines, mandatory corrective plans, and reputational damage. ITAD programs help healthcare organizations meet HIPAA standards by ensuring every device storing PHI is properly sanitized or destroyed.
FACTA
The Fair and Accurate Credit Transactions Act (FACTA) mandates secure disposal of consumer financial information. Organizations must take “reasonable measures” to prevent unauthorized access.
Certified ITAD ensures that financial data is destroyed according to these legal obligations, protecting your organization from potential liability.
GDPR
The General Data Protection Regulation (GDPR) governs the personal data of EU residents. Improper deletion or disposal can result in penalties of up to 4% of global annual revenue.
Following GDPR compliance, including secure ITAD and NIST 800-88 guidelines, ensures sensitive personal data is irrecoverably erased.
DOD
The Department of Defense (DOD) establishes standards for the secure disposal of classified and sensitive government information. ITAD providers offering DOD-compliant destruction ensure that retired devices meet these rigorous requirements, protecting organizations that handle government data from security and legal risks.
EPA
The Environmental Protection Agency (EPA) regulates environmentally responsible recycling and disposal practices. Proper ITAD programs ensure that devices are disposed of or recycled sustainably, reducing environmental impact and demonstrating corporate responsibility.
NIST
The National Institute of Standards and Technology (NIST) 800-88 standard provides detailed guidance for data sanitization, outlining methods for clearing, purging, and destroying storage media. Adhering to NIST 800-88 ensures data is irrecoverable and supports compliance with industry regulations and internal security policies.
The takeaway? Compliance depends on an airtight ITAD.
Industries That Need ITAD
While every organization that stores or processes data should have an ITAD strategy, some industries face elevated risks, stricter regulations, and harsher consequences for mishandling retired technology. These sectors depend on ITAD not just for efficiency, but for legal protection, reputation management, and security.
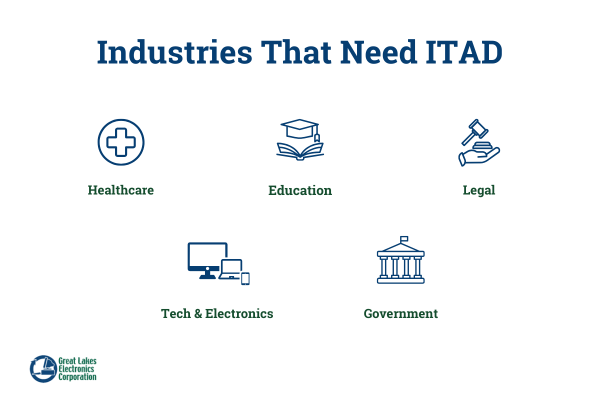
Healthcare
Healthcare organizations handle some of the most sensitive data that exists, including patient records, diagnoses, imaging, and billing information. HIPAA requires secure destruction, documented chains of custody, and verified data sanitization.
A single improperly discarded device can lead to severe fines and damaged trust. For healthcare providers, ITAD is not a choice; it’s a compliance mandate.
Education
School systems, universities, and research institutions store student information, financial aid data, and proprietary academic research. As devices cycle through students, teachers, and administrators, unmanaged endpoints become major vulnerabilities.
Consequently, ITAD ensures outdated laptops, tablets, and lab equipment are wiped, tracked, and retired without putting student privacy or research integrity at risk.
Legal
Law firms and legal departments handle case files, privileged communications, discovery documents, and personally identifiable information (PII). A single compromised drive could expose clients, violate ethical standards, and jeopardize ongoing cases.
ITAD processes also help create a defensible, documented approach to data destruction, maintaining client confidentiality at every step.
Tech & Electronics
Technology companies often store source code, intellectual property, device prototypes, customer data, and product roadmaps. Outdated devices, even those believed to be wiped, may still contain fragments of sensitive data.
ITAD supports secure sanitization, environmentally responsible recycling, and recovery of residual value, all while protecting innovation pipelines.
Government
Public sector agencies manage classified records, infrastructure data, public service information, and citizen-identifiable data. The stakes are higher here: improper disposal can lead to national security risks, loss of public trust, or compliance violations.
Rigorous ITAD ensures devices are controlled, tracked, and destroyed according to federal standards.
What Needs ITAD?
From small offices to global enterprises, every IT asset can carry sensitive information, and every retired device is a potential liability if not managed properly.
Let’s break it down.
1. Servers
Servers store massive volumes of sensitive information, from financial records to proprietary business data. Decommissioning them without proper sanitization is extremely risky.
Certified ITAD ensures that servers are securely wiped, dismantled, or destroyed, preventing data recovery and mitigating potential breaches.
2. Computers
Laptops, desktops, and workstations may seem harmless once retired, but they often contain caches, logs, stored passwords, and hidden files. Even a “clean” machine can still hold recoverable data, making it a goldmine for cybercriminals.
Proper ITAD processes protect your organization by erasing all traces of sensitive information before devices leave your control.
3. Mobile Devices
With the rise of remote work, phones, tablets, and laptops are used by employees outside the office. These devices are especially vulnerable to theft, loss, or misuse if not handled through structured ITAD workflows.
Failing to include mobile assets in your ITAD program is like leaving your front door unlocked for hackers.
4. Data Centers
Data center decommissioning is complex. It involves not only servers but also networking gear, storage devices, cables, and other infrastructure.
Only certified ITAD providers should handle these environments. Professional management ensures full data destruction, compliance, and environmental responsibility.
How to Choose an ITAD Partner
Not all ITAD vendors are created equal. Some promise security but fall short, leaving your data and your business exposed.
Choosing the right ITAD partner is critical to protect sensitive information, stay compliant, and recover value from your retired assets.
Here’s how to make the best choice.
1. Certifications Matter
Firstly, a trustworthy ITAD vendor should have recognized certifications like R2, e-Stewards, and ISO.
These standards prove the vendor follows industry best practices for secure disposal and environmental responsibility. Without certifications, you’re taking an unnecessary risk.
2. Data Destruction Compliance
Never compromise on data destruction standards. A vendor who follows NIST 800-88 guidelines ensures that data is completely unrecoverable, even with advanced forensic tools.
If your ITAD partner doesn’t adhere to this standard, your business is vulnerable to breaches and regulatory penalties.
3. Secure Chain-of-Custody Tracking
Every device must be monitored from the moment it leaves your possession to its final destruction. Chain-of-custody tracking provides full visibility, documenting each step of the process.
This not only ensures accountability but also protects your company in case of audits or legal scrutiny.
4. Environmental Sustainability
Responsible ITAD goes beyond data protection; it includes eco-friendly disposal. Choose a partner that recycles electronics, reuses components, and minimizes landfill waste.
Not only does this reduce your environmental footprint, but it also enhances your brand reputation in a world increasingly focused on sustainability.
5. Detailed Reporting and Certificates of Destruction
Documentation is not optional. Therefore, your ITAD partner should provide comprehensive reports and official certificates of destruction for every device.
These certificates are proof of compliance and demonstrate due diligence to regulators, clients, and internal stakeholders. No documentation means no accountability, and no protection.
Protect Your Business with ITAD
Your organization’s security doesn’t end when technology stops working. In fact, the risk often begins at the end of life.
Above all, you need a process that’s reliable, auditable, compliant, and secure at every step. A professional ITAD partner ensures your business stays protected, no matter how many devices you retire, recycle, or replace.
As you’ve seen, secure IT asset disposition isn’t just another IT responsibility; it’s a powerful shield that protects your data, reputation, and bottom line. Every device you retire carries risk, and every risk demands a strong, compliant ITAD program.
Are your current processes strong enough to protect your business from data exposure, lawsuits, and compliance issues?
If you’re ready to eliminate risk and build a secure, streamlined ITAD program, our team is here to help. We specialize in IT asset disposition that protects data, recovers value, and ensures total compliance from start to finish.
Contact us today to safeguard your business with a proven ITAD strategy built for long-term security and peace of mind.