In today’s data-driven world, the flow of information and technology is vital to so many different things. From how organizations conduct business to healthcare, payroll, and security, tech touches everything.
These things working together do provide significant benefits, but they also have unique problems. Two of these include their use of rare earth metals and the security of disposing items that contain sensitive information.
This has led to the rise of things such as hardware asset management (HAM), there are many best practices that you may (or may not) be aware of regarding HAM, we’re going to cover how GLEC can help you properly facilitate the disposing of your old tech to make room for the new.
What defines hardware and assets?
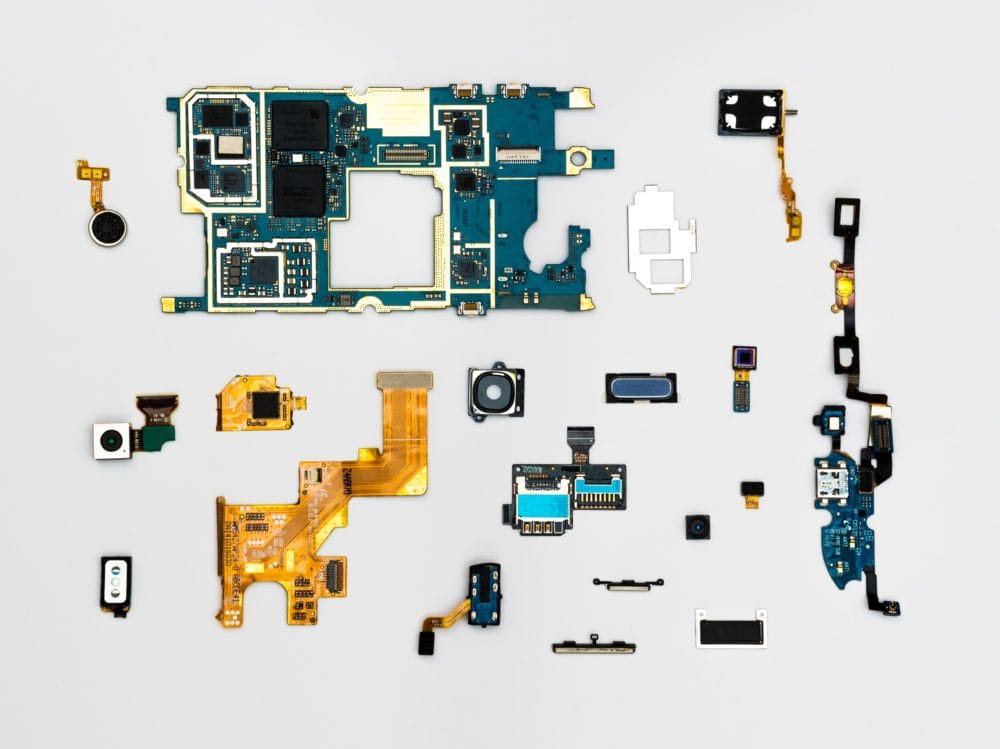
If you want to paint using broad strokes, you can call it E-waste.
To be more specific, it could be any IT asset. That includes retired and obsolete IT equipment, electronics, decommissioned IT equipment, excess IT equipment; that consists of any digital technology that stores or displays data.
Here are some examples of we’re talking about:
- Hard drives
- Computers
- Monitors
- Wi-Fi Routers
- Cameras
- CDs
- Flash drives
- Anything else electronic that potentially stores or processes data
Note*: Software Asset Management (SAM) goes hand in hand with hardware management because software has to run on hardware. Your organization should also devise plans regarding software management as well.
Basic Tenets of Hardware Asset Management
Each organization should have its HAM plan to deal with IT equipment that is no longer needed. Following an HAM plan is a safe procedure for securing sensitive data when doing inventory and getting new office equipment. The “out with the old and in with the new” is what drives business in terms of technology.
However, disposing of assets responsibly, safely and in an environmentally friendly way should be a major concern, and part of the HAM process as well. While factors such as industry and the hardware itself will impact overall plans, there is one basic tenet that you must incorporate into your inventory plan. Security.
You may not realize it, but before you can’t just dispose of your unwanted IT assets, they have to be prepared for disposal through sanitation or destruction. You shouldn’t and in some cases can’t just throw old tech into the trash.
Is Hardware Asset Management necessary?
Simply put, yes. Electronics shouldn’t go to the dump, destroying the data in your computers and other hardware doesn’t mean that they can now be disposed of in the trash with other waste. It only protects your information from would-be hackers and data thieves; now, your materials are ready to be recycled properly. This is especially important in healthcare.
Aside from the environmental aspects of disposing e waste in the trash with other materials, the data breach aspect is another huge problem, and it happens more than you think. It’s a growing problem that’s only getting worse.
In fact, according to the National Conference of State Legislatures, there are at least 35 states and Puerto Rico that have enacted business e waste laws. These laws require private or municipal entities to destroy their data entirely. If you don’t prepare and recycle your unwanted and old tech hardware, you can be held legally responsible for data and privacy breaches.

Success loves preparation
The best way to prepare your depleted or obsolete assets for proper disposal is to remove all data from the device, also called sanitizing. Methods for sanitizing vary by machine. It is highly recommended that no matter what device or type of data you’re working with being backed up on some form of secondary storage.
Examples of storage data backup devices include CDs, DVDs, flash and removable hard drives as well as digital storage options like cloud-based operating systems.

Methods for Data Sanitization
The U.S. Department of Homeland Security lists these methods to help you prepare your devices and electronics for disposal/recycling:
1. Deleting data
Removing data from your device can be one method of sanitization. When you delete files from a device—although the files may appear to have been removed—data remains on the media even after a delete or format command is executed. Do not rely solely on the deletion method you routinely use, such as moving a file to the trash or recycle bin or selecting “delete” from the menu. Even if you empty the trash, the deleted files are still on the device and can be retrieved. Permanent data deletion requires several steps.
Computers
Use a disk cleaning software designed to permanently remove the data stored on a computer hard drive to prevent the possibility of recovery.
Secure erase
A secure erase is a set of commands in the firmware of most computer hard drives. If you select a program that runs the secure erase command set, it will delete the data by overwriting all areas of the hard drive.
Disk wiping
Disk wiping is a type of utility that erases sensitive information on hard drives and securely wipes flash drives and secure digital cards.
Smartphones and tablets
Ensure that all data is removed from your device by performing a “hard reset.” This will return the device to its original factory settings. Each device has a different hard reset procedure, but most smartphones and tablets can be reset through their settings. Physically remove the memory card and the subscriber identity module card (SIM card), if your device has one.
Digital Cameras, Media Players, and Gaming Consoles
Perform a standard factory reset (i.e., a hard reset) and physically remove the hard drive or memory card.
Office equipment
(e.g., copiers, printers, fax machines, multifunction devices)
Remove any memory cards from the equipment. Perform a full manufacture reset to restore the equipment to its factory default.
2. Overwriting
Another method of sanitization is to delete sensitive information and write new binary data over it. Using random data instead of easily identifiable patterns makes it harder for attackers to discover the original information underneath. Data stored on a computer is written in binary code or strings of 0s and 1s. Because of this, one method of overwriting is to zero-fill a hard disk and select programs that use all zeros in the last layer. Users should overwrite the entire hard drive. Then add multiple layers of new data (three to seven passes of new binary data) to prevent attackers from obtaining the original data.
Cipher.exe
A built-in command-line tool in Microsoft Windows operating systems that can be used to encrypt or decrypt data on New Technology File System drives. This tool also securely deletes data by overwriting it.
Clearing
A level of media sanitation that does not allow information to be retrieved by data, disk, or file recovery utilities. The National Institute of Standards and Technology (NIST) notes that devices must be resistant to keystroke recovery attempts. This can be done from standard input devices like a keyboard or mouse and data scavenging tools.
3. Destroying
At our secure facilities, we provide Certified Data Destruction services. We recycle your obsolete and retired electronics in an environmentally responsible manner. Our services also eliminate the environmental and data liability associated with the improper disposal of electronic equipment and data devices.
Magnetic Media Degaussers
Degaussers expose devices to strong magnetic fields that remove the data magnetically stored on traditional magnetic media.
Note*: Degaussing does have some shortcomings. Mainly, it leaves the device intact, which may invite thieves to try and steal the device. If your degausser isn’t correctly calibrated or there is any level of human error during the process, a thief may be able to recover data from your machine.
Solid-State Destruction
The destruction of all data storage chip memory by crushing, shredding, or disintegration is called solid-state destructioRecyclin. Solid-State Drives should be destroyed with devices that are specifically engineered for this purpose.
CD and DVD destruction
Many office and home paper shredders can shred CDs and DVDs (be sure to check that the shredder you are using can shred CDs and DVDs before attempting this method).
Need Help?
In our modern, technology-driven world, business electronics can cause as many problems as they can help with. If you want assistance with liability reduction and the entire tech data recycling process, we’re here to help.
Great Lakes Electronics Corporation will assist you in the processing and recycling of your hardware asset management process to ensure a proper, environmentally-friendly, and secure disposal.
Ready to build your HAM procedure? We can help, simply call us or click here to fill out our contact form. For more information about handling your E waste recycling, learn more about our asset management service.